Privacy Security
Alloomi gives you complete control over your data:
- Access Controls: Choose exactly which platforms and data Alloomi can access
- Data Retention: Configure how long Alloomi retains processed data
- Delete Anytime: Delete all your data at any time with one click
- Export: Export all your data in standard formats
We believe privacy and intelligence aren’t mutually exclusive. You should never have to choose between powerful AI capabilities and data control. Alloomi delivers both.
🔐 Our Privacy Principles
Local-First
Your data stays on your device. Alloomi only accesses minimum required data.
End-to-End Encryption
AES-256 encryption with hardware-isolated processing environments.
Zero Training
Your data will never train public AI models—now or ever. Legally guaranteed.
Auditable
Tamper-proof audit logs. SOC 2 compliance certification in progress.
Local-First Architecture
Your original messages and files stay on your device. Alloomi only accesses the minimum data needed to complete tasks—no unnecessary uploads.
- On the desktop app, raw data never leaves your local environment
- Only processed results are transmitted when needed
- Complete control over what data Alloomi can access
End-to-End Encryption
All authorized data is encrypted with AES-256 industry standard, processed in hardware-isolated trusted execution environments—completely inaccessible to external parties.
- AES-256 encryption for all stored data
- Hardware-isolated trusted execution environments
- Zero visibility into your raw data
Zero Training Commitment
Your data will never be used to train public AI models—now or ever. In writing, legally guaranteed.
- Explicit legal commitment in our terms of service
- No use of your data for model training
- Full transparency on data usage
Auditable Compliance
All critical operations are logged in tamper-proof audit logs. SOC 2 compliance certification in progress.
- Complete audit trail of all data access
- Enterprise-grade security standards
You can view exactly when and why Alloomi accessed your data. Every access is logged with:
- Time: When the data was accessed
- Platform: Which platform (Telegram, WhatsApp, Gmail, etc.)
- Data Type: What kind of data was accessed
- Reason: Why the access was needed (e.g., “Generating insights”, “Replying to messages”)
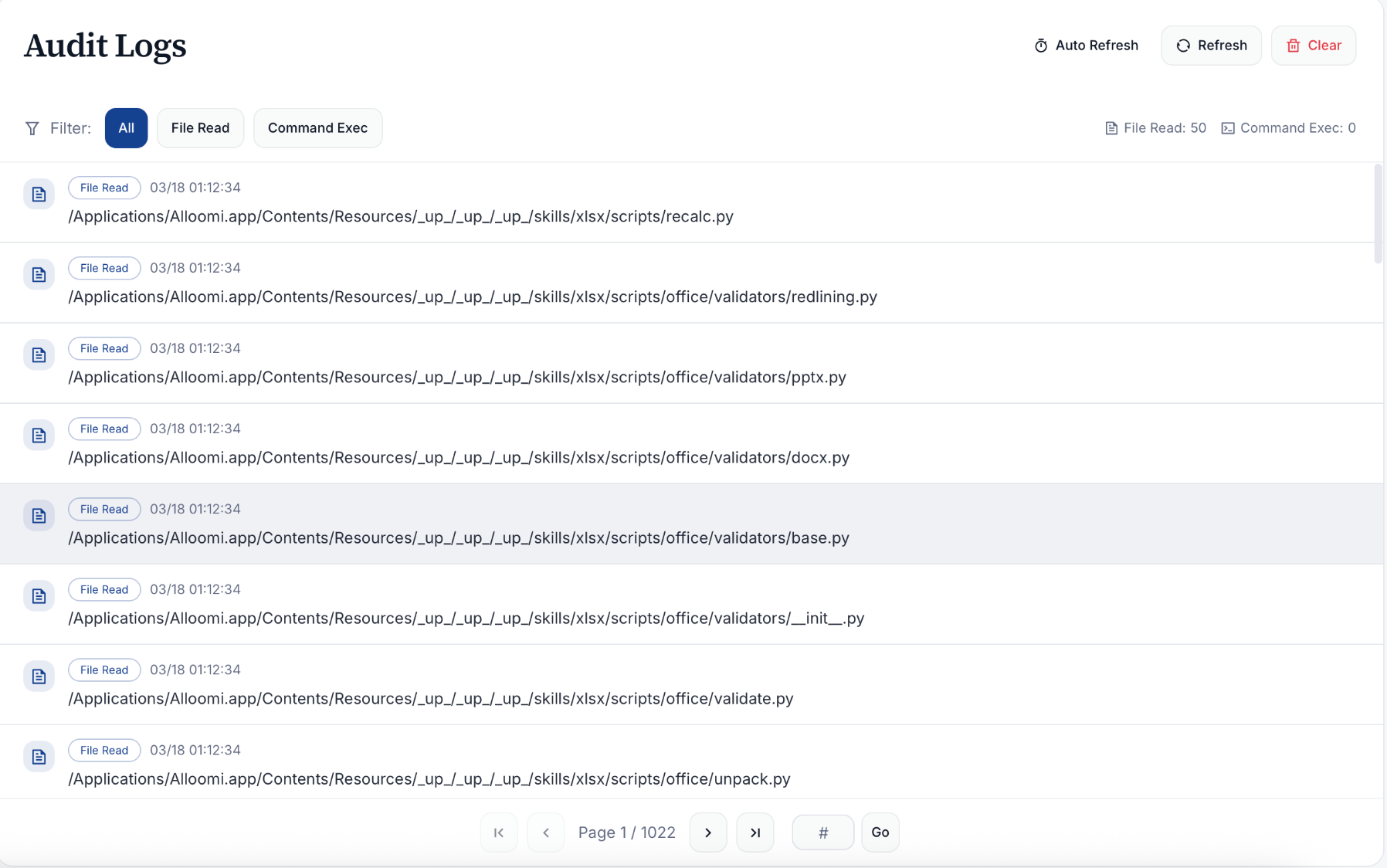
💡 Transparency First: You have full visibility into all data access. If you notice any suspicious activity, you can revoke access immediately from Settings.